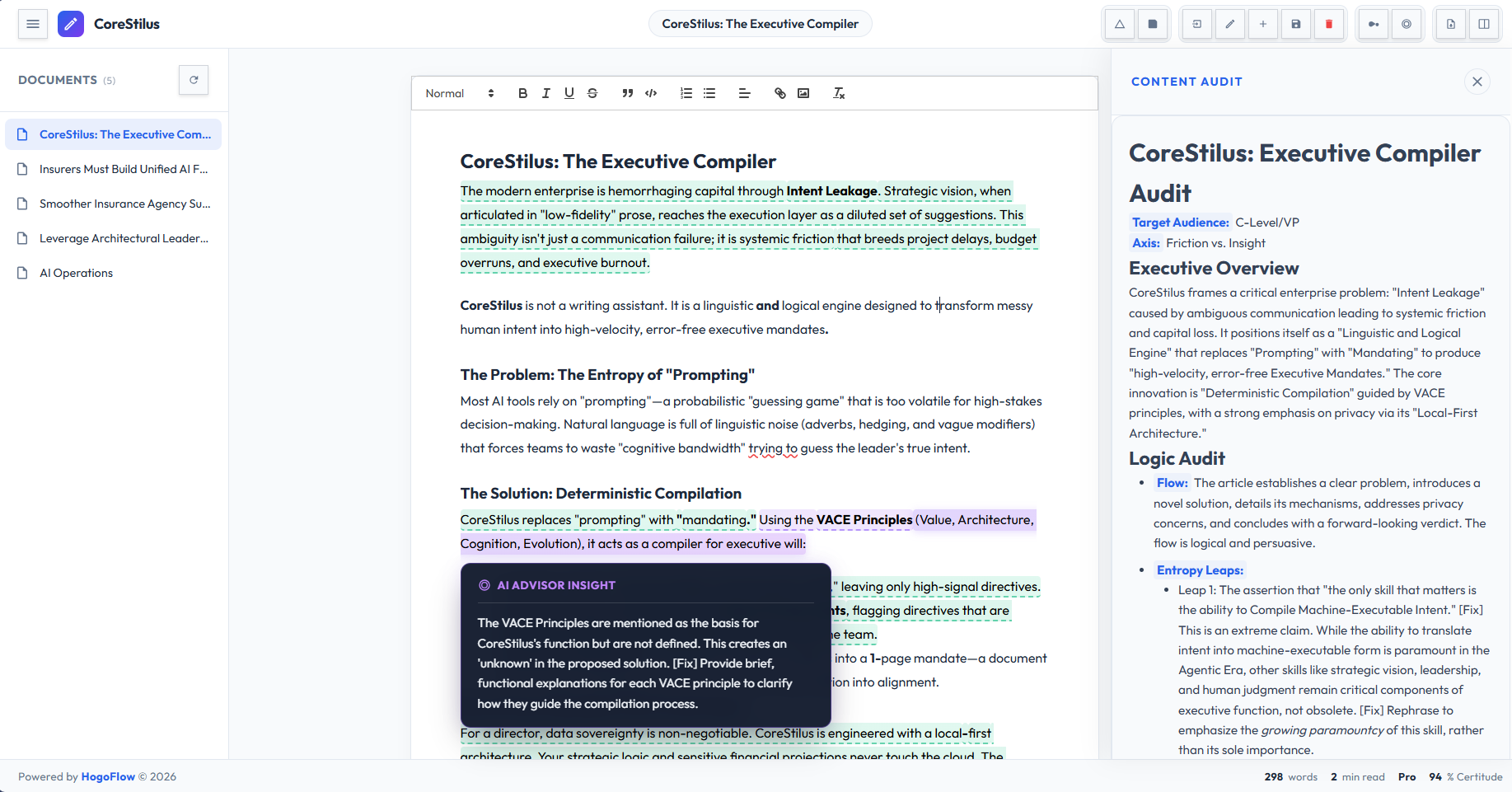
Turn Messy Drafts Into
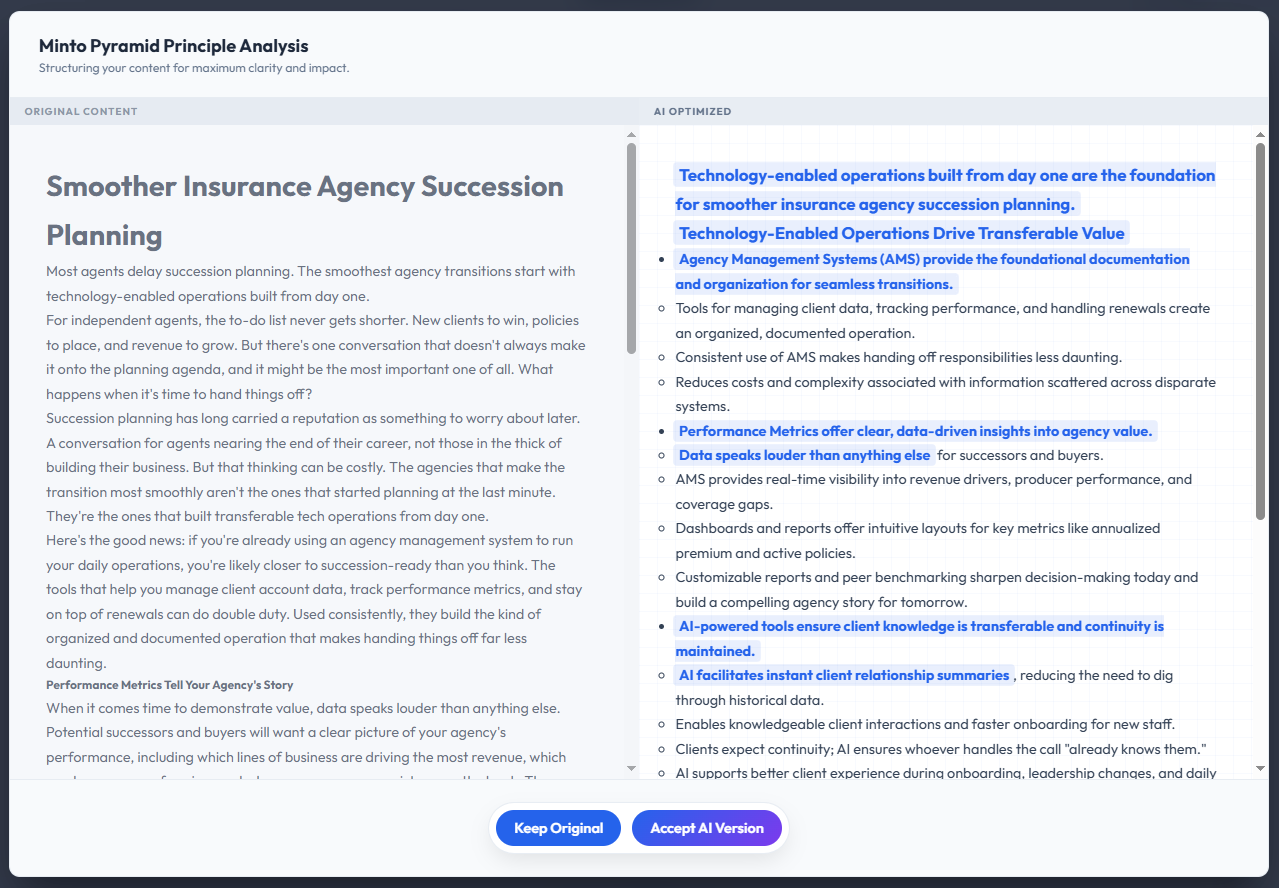
One-Page Mandates
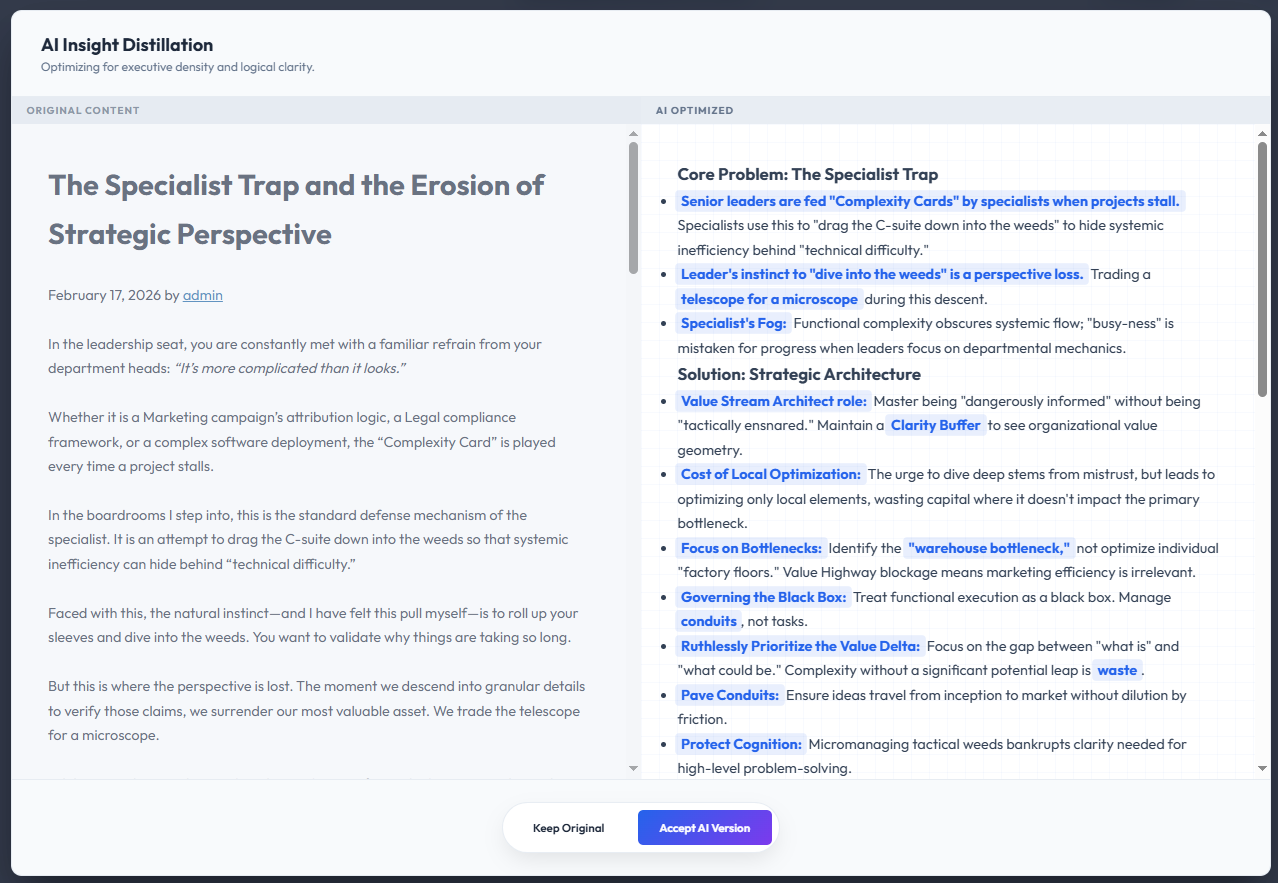
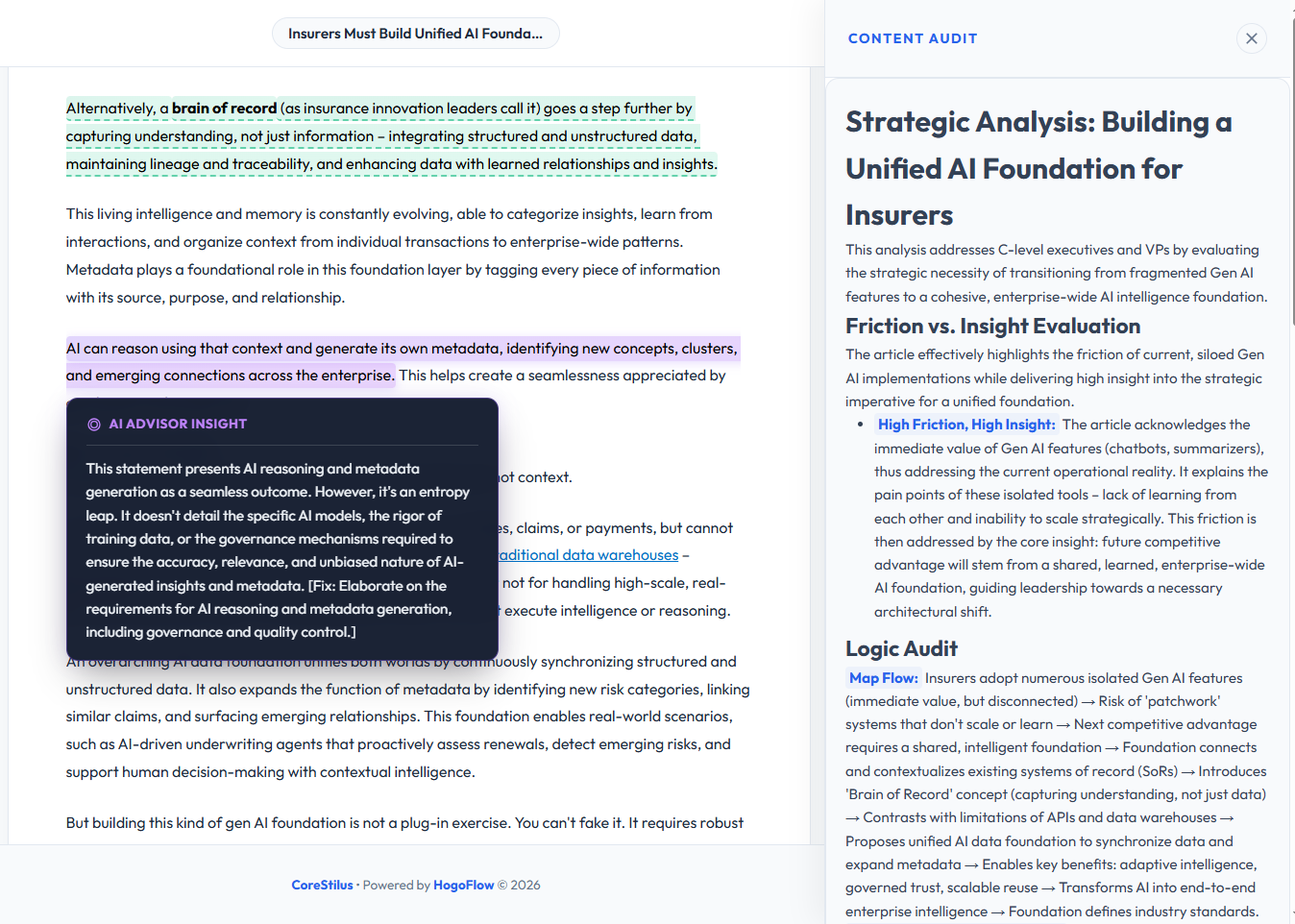
Writing long documents is a system design flaw. We built a logic foundry that extracts your hard truths and forces the conclusion to the top. Protect your time and their attention.